In 2006 the AIDS epidemic was a quarter-century old. Officially starting in June 1981 as a mysterious and fatal disease exclusively found in several dozen young white gay men from New York City and Los Angeles, the disease has already killed 20 million people with 40 million more currently infected with the human immunodeficiency virus (HIV), widely accepted as the sole cause of AIDS. One million Americans are now infected with HIV; and almost half of the new cases are African-American.
The disease was first uncovered in homosexual men from Manhattan. “Gay cancer,” in the form of Kaposi’s sarcoma skin tumours, was the most striking telltale sign; and drugs, promiscuity, and anal sex were all thought to play a role in the unprecedented suppression of the immune system. It was soon obvious that the disease was not limited to gays: the mysterious agent was in the national blood supply, and an epidemic of AIDS was also uncovered in Central Africa.
In April 1984 Robert Gallo of the US National Cancer Institute (NCI) announced his discovery of HIV as the cause of AIDS. Subsequently, Luc Montagnier of the Pasteur Institute in Paris filed a lawsuit claiming he had first discovered the AIDS virus at Pasteur, and that Gallo had stolen the French virus after it was sent to his lab for study.
Twenty-five years later, the origin of AIDS still remains a mystery. The disease is widely believed to have originated in Africa when a primate (monkey) virus “jumped species” to first infect Black Africans. However, it is important to note that this belief is theory, not proven fact.
Montagnier has wisely cautioned that it is extremely important to distinguish between the ancestral origin of HIV and the actual beginning of the AIDS epidemic. The animal virus ancestor of HIV may indeed be centuries old, but it is obvious that the epidemic itself is new.
The epidemic did not begin in Africa. The first AIDS cases were uncovered in Manhattan in 1979. At that time there were no reported African cases. In fact, the AIDS epidemic in Africa did not begin until the autumn of 1982 at the earliest.
How was HIV introduced exclusively into the gay community in the late 1970s? The exclusive introduction of HIV into the homosexual population of New York City is an unprecedented event in the history of medicine. This biologic phenomenon has never been fully explained scientifically. There is certainly no evidence to indicate white gay men were the only people exposed to sexual contact with Africans, particularly at a time when the epidemic did not exist in Africa. Furthermore, it is biologically impossible for a purported sexually-transmitted and blood borne “virus out of Africa” to infect only young, white, healthy men in Manhattan! Yet, the impossible did happen. Despite these facts, we are repeatedly told that AIDS began in Africa, even though the American epidemic began before the African epidemic.
The mixing of AIDS facts and fallacies has long been apparent to researchers like myself who are convinced that HIV did not come from Mother Nature and “species jumping,” but was most likely introduced via contaminated vaccine experiments exclusively targeting the Black African and the American Gay community.
Before exploring the man-made theory of AIDS, it is important to note a small but highly vocal group who believes the cause of AIDS is still unknown, that the AIDS blood test is worthless, and that HIV is a harmless virus that is not sexually transmitted. This group, headed by retrovirologist Peter Duesberg and other well-credentialed scientific “dissidents,” believes AIDS is a toxic and nutritional syndrome. They blame AIDS on recreational drug use among gays – and poverty and malnutrition in Africa for the disease.
As a medical doctor and AIDS and cancer researcher, I am certainly not in accord with this group, but they have been quite successful politically, influencing world leaders like President Thabo Mbeki of South Africa, much to the chagrin of the World Health Organisation. For more information, go to www.google.com and type in “VirusMyth” or “The Perth Group”.
Genetic Engineering and the AIDS Epidemic
There is a close connection between the rise of genetic engineering and mixing of viruses in the early 1970s and the outbreak of HIV in the late 1970s. This connection persists in the form of the many unprecedented “emerging diseases” caused by “new viruses” that continue up to the present time.
In 1970 the discovery of a cell enzyme, called “reverse transcriptase” by Howard Temin and David Baltimore, allowed molecular biologists to detect so-called retroviruses in some animal cancers. It was soon recognised that retroviruses could be found normally in the genes of many animal cells, and that scientists could manipulated these viruses to produce detrimental effects on the immune system. In “species jumping” laboratory experiments, many viruses were transferred between different animal species and were also adapted to human cells.
As part of President Richard Nixon’s “War on Cancer,” genetic engineering of viruses became an integral part of the now largely forgotten Special Virus Cancer Program, conducted under the auspices of the NCI. Nixon also transferred part of the Army’s biological warfare unit at Fort Detrick, Maryland, over to the NCI, thereby allowing secret biowarfare experimentation to be carried out under cover of bona fide cancer research.
All this virus transfer and molecular manipulation was a biologic disaster waiting to happen. What would happen if one of these highly dangerous genetic creations escaped from the laboratory into the public sector? This culminated in a historic conference entitled “Biohazards in Biological Research” held at Asilomar, near Pacific Grove in California in 1973. Despite the biologic dangers, it was decided to continue this research.
By the late-1970s the War against Cancer and the Virus Cancer Program proved a bust with no cancer-causing retroviruses found in humans. The Program was winding down in 1978, at the exact time when government scientists were also enrolling thousands of gay men in New York City to serve as guinea pigs in the hepatitis B experiment that took place that same year at the New York Blood Centre in Manhattan. In 1979 the first cases of AIDS in gay men were reported from Manhattan. Coincidence? I think not.
Five years later, Gallo, who had worked for the Virus Cancer Program (VCP), “discovered” the retrovirus that causes AIDS; and Duesberg, who also worked for the VCP, continues to declare that HIV is harmless.
Is there a connection between the laboratory manipulation of primate retroviruses in the 1970s and the outbreak of AIDS? Or did Mother Nature conveniently pick that exact time to jump monkey genes into gay men to spectacularly revive the science of retrovirology and the careers of virologists like Gallo?
The Gay Vaccine Experiment and the Outbreak of AIDS
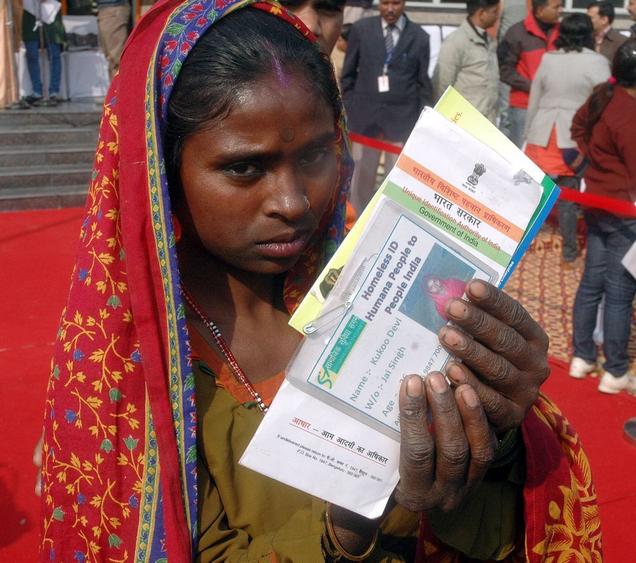
The earliest AIDS cases in America can be clearly traced back to the time period when the hepatitis B experiment began at the New York Blood Centre. The Centre began injecting gay men with multiple doses of the experimental vaccine in November 1978. The inoculations ended in October 1979, less than two years before the official start of the epidemic. Most importantly, the vaccine was developed in chimpanzees – the primate now thought to contain the “ancestor” virus of HIV. Also downplayed is the Centre’s pre-AIDS connection to primate research in Africa and also to a primate centre in the New York City area. The final experimental vaccine was also made by Merck and the NIH from the pooled serum specimens of countless gay men who carried the hepatitis B virus in their blood.
The New York Blood Centre (NYBC) is the largest independent blood supplier and distributor in the USA. In 1970, Alfred M Prince, M.D., head of the NYBC Laboratory of Virology, began his hepatitis research with chimps housed at LEMSIP (Laboratory for Experimental Medicine and Surgery) in downstate Tuxedo, NY. Until disbanded in 1997, LEMSIP supplied New York area scientists with primates and primate parts for transplantation and virus research.
Founded in 1965, LEMSIP was affiliated with New York University Medical Centre, where the first cases of AIDS-associated Kaposi’s sarcoma were discovered in 1979. NYU Medical Centre researchers were also heavily involved in the development of the experimental hepatitis B vaccine, and the Centre received government grants and contracts connected with biological warfare research beginning in 1969, according to Dr. Leonard Horowitz, author of Emerging Viruses: AIDS and Ebola (1996).
In 1974 Prince, with the support of Aaron Kellner, President of the NYBC, moved the chimp hepatitis research to a new primate centre called Vilab II in Robertsfield, Liberia, in Africa. Chimps were captured from various parts of West Africa and brought to VILAB. The lab also prides itself by releasing “rehabilitated” chimps back into the wild. One cannot help but wonder if some of the purported “ancestors” of HIV in the African bush have their origin in chimpanzees held in African primate labs for vaccine and medical experimentation.
The hepatitis B experiment, which inoculated over 1,000 healthy gay men, was a huge success with 96% of the men developing antibodies again the hepatitis virus. This high rate of success could not have been achieved if the men were immunosuppressed, because immunosuppressed people do not easily form antibodies to the vaccine. The experiment was followed by similar hepatitis B experiments using gay men in Los Angeles, San Francisco, Chicago, Denver and St. Louis, beginning in March 1980 and ending in October 1981, the same year the epidemic became official.
In the mid-1980s the many blood specimens donated by the gay Manhattan men during the experiment were retrospectively examined for HIV infection by researchers at the NYBC. It was determined that 6% of the specimens donated between 1978-1979 were positive for HIV. By 1984 (the end of the study period) over 40% of the men tested positive for HIV.
The final fate of all the men in the experiment has never been revealed. However, the blood donated by these men are the oldest HIV-positive blood tests on record in the United States. The full story of this experiment and its aftermath are contained in my two books on man-made AIDS: AIDS and the Doctors of Death (1988), and Queer Blood (1993). One fact is obvious: There was no AIDS in America until the exact year the government began experimenting with gay men.
There is also a suppressed connection between the outbreak of AIDS in Africa and the widespread vaccine programs conducted by the World Health Organisation (WHO) in the 1970s in Central Africa, particularly the smallpox eradication program. On May 11, 1987, London Times science writer Pearce Wright suggested the smallpox vaccine program could have awakened a “dormant” AIDS virus infection in Africa. Gallo was quoted as saying, “The link between the WHO program and the epidemic is an interesting and important hypothesis. I cannot say that it actually happened, but I have been saying for some years that the use of live vaccines, such as that used for smallpox, can activate a dormant infection such as HIV.”
This explosive story linking AIDS to African vaccines was suppressed and never appeared in the controlled major American media. The genocidal and depopulation implications of this suppressed story can be found on the Internet by googling “WHO Murdered Africa”, by William Campbell Douglas, M.D.
Vaccines, Species Jumping and HIV
There are inherent dangers in vaccine production because vaccines are made on living cells. Contamination with bacteria and viruses are constant problems during the manufacturing process. Laboratory additives used to feed the cell cultures (such as fetal bovine [cow] serum) may also be a source of microbial contamination. Some researchers believe living and killed viruses injected into the body can combine with other viruses normally present in the body, resulting in disease-causing “recombinants.” Vaccines can also contain viral particles, as well as newly recognised tiny bacteria known as “nanobacteria.” Half the 2004 flu vaccine supply was destroyed due to contamination with disease-causing bacteria. The dangers of vaccines are downplayed in an attempt to assure the public that vaccines are safe.
We are repeatedly told that HIV is the first primate virus to “jump species” and produce an epidemic in humans. But, in truth, the AIDS epidemic is the secondinstance in which a monkey virus has been transferred to humans via vaccines.
Rarely-publicised is the fact that a cancer-causing monkey virus jumped species a half century ago when contaminated polio vaccines were injected into millions of people, including half the US population of that era. In the early 1960s it was discovered that some lots of polio vaccine manufactured on rhesus monkey kidney cells during the period 1955 to 1963 were contaminated with a monkey virus called SV40 (Simian virus #40). This primate virus was proven to cause cancer in experimental animals. However, to this day, health officials still insist there is no proof that SV40 causes human cancer.
Despite the lack of government interest, genetic and immunologic studies of SV40 by independent researchers over the past decade indicate this virus is clearly associated with rapidly-fatal cancers of the lung (mesothelioma), bone marrow cancer (multiple myeloma), brain tumours in children, and other forms of cancer.
A Washington Times report (September 21, 2003) states, “Some of the polio vaccine given to millions of American children from 1962 until 2000 could have been contaminated with a monkey virus that shows up in some cancers, according to documents and testimony to be delivered to a House committee Wednesday. The vaccine manufacturer said such claims ‘don’t have any validity,’ and the Centres for Disease Control and Prevention (CDC) agrees.” (See the website: www.sv40cancer.com.) For anyone who still believes vaccine makers and health officials always act in your best interest, I would highly recommend a recently published book titled The Virus and the Vaccine: The True Story of a Cancer-Causing Monkey Virus, Contaminated Polio Vaccine, and the Millions of Americans Exposed by Debbie Bookchin and Jim Schumacher.
Medical Experimentation and Biological Warfare
The idea of man-made AIDS is often considered a paranoid belief. Why would scientists introduce a virus to kill millions of people? AIDS experts routinely blame primates and human sexuality for the origin and spread of HIV, but they never consider the possibility that HIV could have originated in an animal cancer virus laboratory.
The sad truth is that governments and the military do indeed experiment on unsuspecting citizens. And Iraqi bioweapons of mass destruction was one of the reasons used to justify the current invasion of Iraq.
It is clear that AIDS started as a “gay disease.” However, yet another downplayed fact is that the HIV “strain” in America is different from the HIV strains found in Africa.
Harvard virologist Max Essex claims the American HIV strain spreads more easily via anal sex; whereas the African strains spread more efficiently via vaginal sex. This could explain why the American epidemic spreads primarily through homosexual activity and anal sex, while in Africa it is primarily heterosexual and spreads through vaginal sex. The “different” HIV strain in America is further evidence that “American AIDS” did not originate in Africa.
The Relationship Between AIDS and Cancer
The relationship between AIDS and cancer is also downplayed, along with the connection between the Special Virus Cancer Program and the ensuing outbreak of HIV. In Gallo’s book he readily admits to a relationship between AIDS and cancer, noting that “many people with AIDS develop one or more cancers.” There is now no doubt that HIV can lead to an increased incidence of cancer, particularly Kaposi’s sarcoma, Hodgkin’s disease, non-Hodgkin’s lymphoma, and cervical cancer.
The purpose of the Virus Cancer Program was two-fold. First, to discover a virus in humans that could cause a form of cancer. Second, to develop immunosuppressive laboratory viruses useful in “making” cancer in experimental animals.
When Gallo discovered HIV in 1984, he called it a cancer-causing “leukemia/lymphoma” virus. The name was quickly changed to a “lymphotropic” virus, thus obscuring the relationship between the new “gay disease” and cancer. Virologists were quickly convinced that the virus came from primates, and both Gallo and Essex heavily promoted the readily accepted African green monkey origin of HIV. A decade later, chimpanzees (rather than monkeys) became the more favoured origin. The primate origin of HIV was further obscured by titling the virus as a “human immunodeficiency virus” (HIV) , rather than calling it “primate immunodeficiency virus” (or PIV) in humans.
Is HIV the Sole Cause of AIDS?
As noted, HIV is believed to be the sole cause of AIDS, although a few AIDS dissidents believe HIV is harmless. Generally disregarded by both groups is the matter of the origin of Kaposi’s sarcoma, the “gay cancer” associated with AIDS.
In 1994 it was reported that KS is actually caused by a new “herpes-8” virus. KS cases were first discovered in the late nineteenth century; and before AIDS it was a rare form of cancer. Before AIDS, KS was a non-transmissible disease that was never seen in young American men.
The finding of a new KS virus indicates that two different viruses were simultaneously introduced into gay men when AIDS began in the late 1970s. No rational explanation has been put forth for this bizarre occurrence; and how this “new” virus could cause a gay epidemic of KS has never been explained satisfactorily. Further complicating the “sole cause” of AIDS scenario is the recent discovery of tiny bacterial forms known as “mycoplasma.” Luc Montagnier believes these microbes are important infectious “co-factors” in the development of AIDS, although most AIDS researchers ignore mycoplasma.
The “Cancer Microbe” Link to AIDS
Although the precise cause of cancer is unknown, there is a century of microbial research linking certain tuberculosis-like bacteria to cancer. This research is ignored as medical heresy, but my own reported cancer studies indicate that “acid-fast” bacteria indeed exist in common forms of cancer and in Kaposi’s sarcoma.
I have written extensively about these bacteria in AIDS; The Mystery & the Solution (1984), The Cancer Microbe (1990), and Four Women Against Cancer(2005). Cancer bacteria have characteristics of both bacteria and viruses. There are also similarities to mycoplasma and to newly-discovered nanobacteria, currently considered to be the smallest forms of life and known to contaminate commercial vaccines. Nanobacteria are ubiquitous and may be involved in the pathology of many diseases currently considered of unknown cause.
Cancer microbe research has been ignored in AIDS and KS. However, Lawrence Broxmeyer, M.D., in AIDS: What the Discoverers of HIV Never Admitted (2003), concludes that the real cause of AIDS is not HIV, but actually tuberculosis-like bacteria. He thinks Gallo and Montagnier found a retrovirus because that was the only thing they were looking for.
Unlike Broxmeyer, I believe HIV came out of animal cancer research and dangerous vaccine and biological warfare experimentation – and that HIV made its way into vaccines injected into African Blacks and American Gays. If unrecognised cancer microbes are proven to be an unrecognised infectious factor in cancer and AIDS, as I believe they are, this would certainly add to the dangers of genetic engineering of cancer viruses and new bio-warfare agents.
I believe HIV is essential to produce the immunodeficiency characteristic of AIDS, but I consider HIV plus unrecognised “cancer bacteria” to be the causes of AIDS.
The Origin of Gallo’s HIV Virus
Could HIV be related to reported virus-like forms of cancer bacteria? A careful reading of how Gallo “isolated” HIV indicates possible derivation from cancerous cells harbouring unrecognised bacteria.
Unlike most bacteria which can be grown on artificial laboratory culture media, viruses need living cells to grow and survive. Pulitzer Prize-winning author John Crewdson provides a detailed analysis of the discovery of HIV in Science Fictions: A Scientific Mystery, A Massive Cover-Up, and the Dark Legacy of Robert Gallo (2002), a highly unflattering portrait of Gallo and an account of the lawsuit initiated by the Pasteur Institute, accusing Gallo of stealing the AIDS virus.
According to Crewdson, HIV was finally isolated in Gallo’s lab by isolating the virus in pooled blood T-cells from ten patients with AIDS. From that brew, the virus was cultured in larger amounts for commercial purposes by growing HIV on “cell lines” derived from the white blood cells (T-cells) of patients with lymphoma cancer. This particular strain of HIV became the basis for Gallo’s patented HIV blood test and the resulting lawsuit.
Montagnier claimed that he first discovered HIV at Pasteur and when he sent the virus to Gallo’s lab for testing, he believes Gallo stole the virus and made it his own discovery. Gallo repeatedly declared his virus was not the French virus.
It was eventually proven that Montagnier’s virus somehow made its way into Gallo’s HIV culture. Just as everyone’s fingerprints are different, so too is every HIV virus. Gallo’s virus was molecularly identical to Montagnier’s in every respect. With the intervention of President Ronald Reagan and the French Premier, the lawsuit was settled out of court in 1987 , with the two researchers agreeing to split the royalties from the AIDS blood test.
Despite all this, the scientific controversy continued, resulting in additional investigations by the National Academy of Sciences and the NIH Office of Scientific Integrity. In 1991, Gallo finally conceded that Montagnier’s virus had most likely contaminated his laboratory and that his AIDS patented blood test was indeed based on the Pasteur virus. In 1992, the National Academy of Sciences’ panel completed its investigation, producing a report critical of Gallo.
All these scientific irregularities surrounding the precise lab origin of HIV point to serious problems in virology. For example, for several years Gallo was unable or unwilling to admit his virus was identical to Montagnier’s virus, even though they proved as identical as any two HIV virus strains could be. Furthermore, the controversy proves how easily virus laboratories can be contaminated by “outside” viruses.
One of the contentions of the man-made theory of AIDS is that the experimental hepatitis B vaccine was contaminated with an immunosuppressive AIDS-causing agent and/or the Kaposi’s sarcoma virus. This theory is condemned as conspiracy theory. Certainly the vaccine was unlike any other in that it was made from the blood of gay men who were hepatitis B virus carriers. During the gay experiment at the NYBC there was concern that something was wrong with the vaccine and that it might be contaminated. According to June Goodfield’sQuest for the Killers, p 86, “This was no theoretical fear, contamination having been suspected in one batch made by the National Institutes of Health, though never in Merck’s.”
Four years before AIDS in 1975, Gallo also reported a “human virus” (HL-23) that subsequently proved to be three contaminating laboratory cancer-causing primate viruses (gibbon ape virus, simian sarcoma virus, and baboon endogenous virus). Gallo claims he has no idea how these animal viruses contaminated his lab. In 1986 Essex also reported a “new AIDS virus” that eventually turned out to be a monkey virus traced back to his own lab. Despite these contaminations, Gallo and Essex both blamed AIDS on monkeys in the jungle and heavily promoted the “out of Africa” origin of American AIDS.
After AIDS began there were instances where a strain of HIV isolated from a particular AIDS patient inadvertently contaminated HIV specimens from other AIDS patients – and where HIV strains sent to other laboratories accidentally contaminated additional specimens.
For years Montagnier insisted that Gallo’s virus was isolated from a French patient named Brugiere. In 1991 the two foremost AIDS experts were astonished to learn that Gallo’s strain of HIV actually belonged to a patient named Laillier. Unbeknownst to Montagnier, the “Bru” culture had somehow contaminated the “Lai” culture at the Pasteur lab.
Is AIDS Genocide Against Gays and Blacks?
Why is there a blackout of the man-made theory of AIDS in the scientific literature and in the corporate-controlled media? Although some evidence is presented here, it is a fraction of the documentation presented in my two books on the man-made epidemic, and in books by Dr. Leonard Horowitz, and Professor Robert E Lee, and in Dr. Robert Strecker’s video “The Strecker Memorandum”, and in other sources.
I do not believe the exclusive introduction of HIV into the most hated minority in America was caused by monkeys in the African bush, particularly when AIDS appeared immediately after the gay experiment. Why are primates in the African wild blamed when tens of thousands of captive primates in virus labs all over the world have been injected with infectious viruses and cancerous tissue for more than a century?
Why were African Blacks targeted? Many Africans and African-Americans believe AIDS is an experiment to rid the world of Black people, as part of a government-sanctioned world depopulation program.
American gays were the perfect target to test a new retrovirus. A largely homophobic public would easily accept HIV infection in gays, due to their purported promiscuity and drug use. Few people would believe the US government would secretly test biologic agents on its civilians, although there is a well-documented history of secret unethical experimentation extending back to the Cold War of the 1950s which includes the government’s horrendous “radiation experiments.”
I cannot explain the silence and apathy on these issues from the Black and the Gay communities. People don’t seem to care much about genocide unless their own group is affected; and even so, most people are in denial and don’t want to know about man-made AIDS. Many AIDS activists simply dismiss the man-made theory as a “distraction” which interferes with HIV testing and treatment, and the search for a cure.
The Secret History of AIDS
The history of AIDS has been deliberately white-washed to obscure its man-made origin. Knowledge of HIV and other retroviruses came directly out of the little-known and secret Special Virus Cancer Program of the 1970s. More than one virus was introduced into American gays in the late 1970s, and mycoplasma and “cancer bacteria” are additional infectious agents that have been ignored in proclaiming HIV as the “sole cause of AIDS.”
Secret bio-warfare research co-mingled with bona fide cancer research at the NCI in the decade before AIDS, and that association continues up to the present time. AIDS in America erupted when government researchers began experimenting with gays, using an experimental vaccine developed in primates – the animals purported to contain the “ancestor virus” of HIV. AIDS in America did not come from Africa. HIV occurred exclusively in the gay community because the virus was put there by the “hand of man.”
Mother Nature wisely separated the species but, in the decade before AIDS, genetic researchers repeatedly violated the “species barrier” by transferring cancer-causing viruses between various animal species, ostensibly to improve our health.
The man-made theory of AIDS is not based on conspiracy theory. The theory warrants a full scientific investigation – and the secret history of HIV and AIDS needs to come out of the closet.
ALAN CANTWELL MD is a retired physician and cancer researcher who believes cancer is caused by bacteria and AIDS is man-made. There is probably no other physician on the planet whose publications are as controversial. Dr. Cantwell is a frequent contributor to New Dawn. Much of his research can be found on google.com, and thirty of his published papers can be accessed at www.ncbi.nlm.nih.gov/PubMed/ (type in Cantwell AR). He is the author of two books on the man-made epidemic of AIDS: AIDS and the Doctors of Death, and Queer Blood, and a book on the microbiology of cancer, The Cancer Microbe. His latest book is called Four Women Against Cancer. Dr. Cantwell is now happily retired from the clinical practice of dermatology, and lives in Hollywood, California. Web site: www.ariesrisingpress.com Email: AlanRCan@aol.com.